Mobile edge computing (MEC), also known as multi-access edge computing or simply multi-access computing, is a crucial component of the intersection between the Internet of Things (IoT) and mobile devices. MEC differs from processing data on mobile devices by focusing on processing data closer to its source.
Instead of transmitting data to the cloud, MEC leverages edge computing resources like nearby servers or cell towers. Given its emphasis on mobile (i.e., wireless) devices, the European Telecommunications Standards Institute (ETSI) plays a significant role in the development of MEC.
This piece provides an overview of ETSI MEC standards, explores the functioning of MEC, highlights various MEC application scenarios identified by ETSI, and delves into the security challenges associated with MEC.
The ETSI MEC Industry Specification Group (ISG) is tasked with establishing the MEC standardization environment to facilitate application integration across diverse MEC platforms from multiple vendors.
The standards developed by the ISG are created in collaboration with the OpenFog Consortium. MEC falls under the umbrella of edge computing for mobile devices, while fog computing represents a distributed computing architecture bridging the edge to the cloud, as depicted in Figure 1.
The ISG standards aim to connect devices with computing services within the 5G radio access network (RAN). These standards cover the architectural framework, technical requirements, application protocol interfaces (APIs), terminology, and management protocols. Several management standards enable functions such as creating, managing, and deleting MEC applications on the edge network.
How MEC Operates
MEC is designed to complement cloud computing, enhance application performance, reduce response times and network congestion, and optimize bandwidth efficiency. Instead of transmitting large volumes of data to the cloud, MEC conducts initial processing on edge servers in base stations. Subsequently, data may be sent to the cloud for further processing and analysis to deliver optimal performance to mobile users, as illustrated in Figure 2.
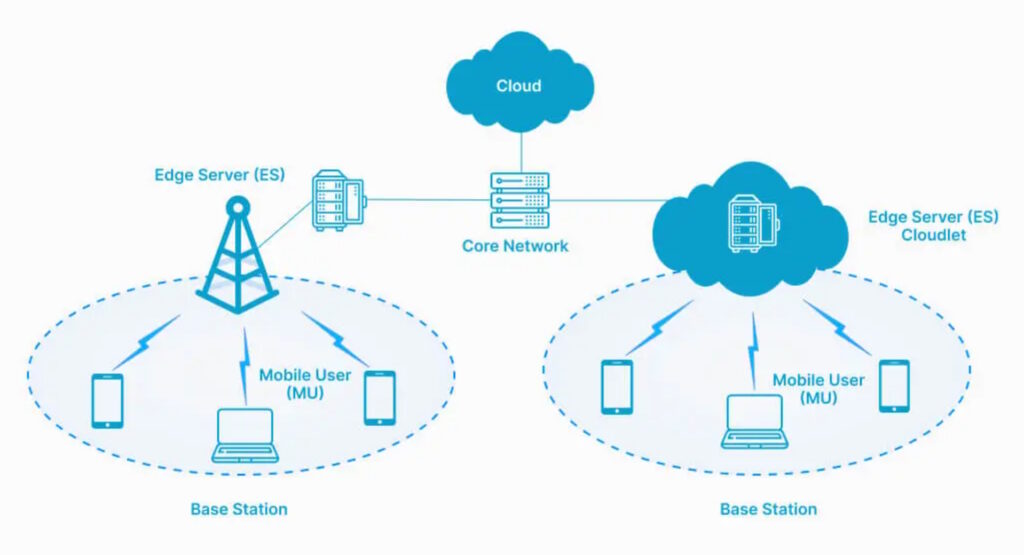
Figure 2. MEC relies on edge servers and other computing resources in base stations. (Image: NYBSYS)
One of the initial MEC applications identified by ETSI was vehicle-to-everything (V2X) connectivity. Since then, the scope of potential MEC applications has expanded to encompass drones, autonomous vehicles, Industrial IoT (IIoT), smart manufacturing, gaming, smart grid, video analytics, location services, optimized local content distribution, and data caching.
The diverse array of MEC services introduces a variety of security challenges.
Security Challenges in MEC
MEC presents a complex security landscape. An analysis has identified three primary MEC attack surfaces with various vulnerabilities, including:
- Insecure backhaul
- Shared infrastructure with third-party applications
- Attacks from the public Internet

Figure 3. Three areas of security concern for MEC are mobile backhaul, third-party applications, and the public Internet. (Image: Juniper Networks)
An insecure backhaul is vulnerable to man-in-the-middle (MIM) attacks, eavesdropping, data interception, and other security risks. To mitigate these threats, the 3GPP introduced the concept of a security gateway (SecGW) that enables mutual authentications between base stations and core networks. Two key 3GPP specifications associated with the SecGW are:
3GPP 33.210: defines the security architecture for network domain IP-based control planes, encompassing control signaling between elements of Network Domain Security over Internet Protocol (NDS/IP) networks and serving as a central repository for cryptographic profiles for security above the IP layer.
3GPP 33.310: offers a common IP Multimedia Subsystem (IMS) specification covering various radio technologies like 2G, 3G, LTE, 5G, and potentially 6G. It includes details on interconnect agreements, which are agreements between two operators to establish secure communications.
Even authorized third-party applications can introduce security risks. MEC employs virtual network functions (VNFs) to reduce this vulnerability. VNFs can handle routing, firewalling, load balancing, network address translation (NAT), and more.
Enhancing security for third-party applications within the MEC edge cloud can be achieved through micro-segmentation based on a zero-trust architecture. Micro-segmentation partitions the network into isolated segments and applies precise access controls and policies to each segment.
Furthermore, the connection to the public internet poses a third attack surface susceptible to common attacks like spoofing and eavesdropping. Security measures such as a stateful firewall capable of understanding network connection context can safeguard against sophisticated attacks.
Distributed Denial of Service (DDoS) protection can monitor network traffic patterns for suspicious activity and automatically take measures to filter or redirect malicious traffic, ensuring uninterrupted operations.
Conclusion
MEC relocates data processing from the cloud to base stations in close proximity to the application to enhance response times, alleviate network congestion, and optimize bandwidth efficiency. The ETSI ISG plays a pivotal role in shaping MEC standards, while the 3GPP has developed relevant security protocols.
References
5G Edge Cloud and Multi-access Edge Computing (MEC) Security, Juniper Networks
Demystifying Mobile Edge Computing, Appinventiv
How Does MEC Work?, NYBSYS
Mobile Edge Computing, Hewlett Packard Enterprise
Multi-access Edge Computing (MEC), ETSI
What is edge computing?, Microsoft
What’s the Difference Between MEC and Fog Computing?, SDxCentral
EEWorld Online related content
Orchestration at the edge reduces network latency
Platform management interface specification covers COM-HPC-based edge computing designs
Edge computing security: Challenges and techniques
Open-source edge computing platform now supports AI, computer vision
Exceptions, traps and interrupts, what’s the difference?