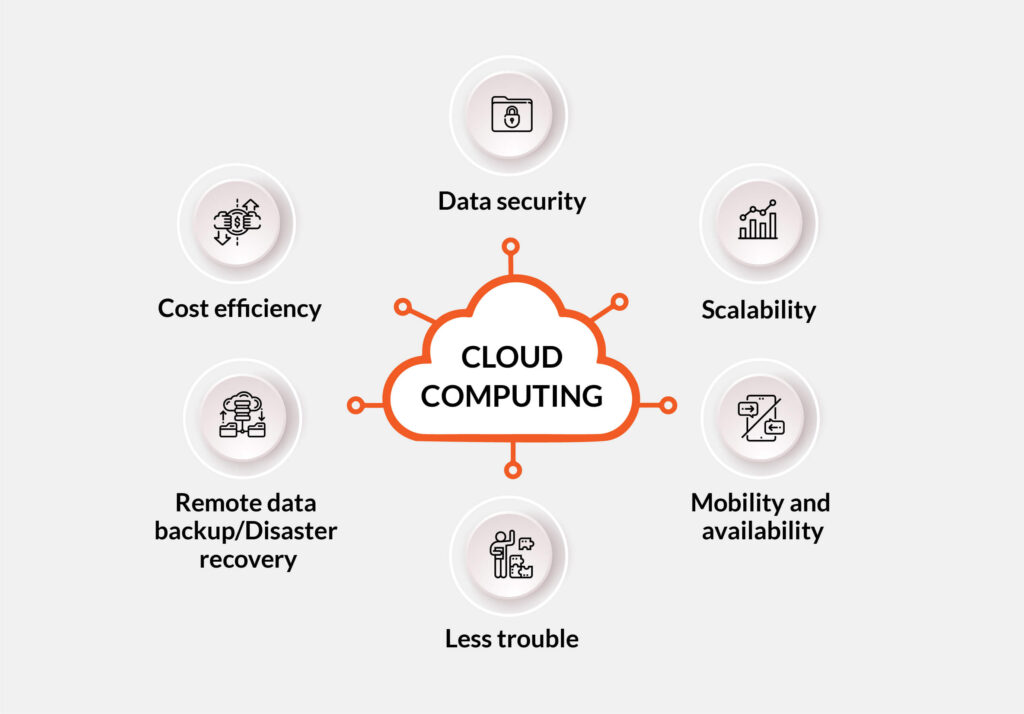
Cloud storage and computing offer numerous benefits to businesses, but there is a common misconception that simply transitioning to cloud storage guarantees data security. However, securing data in the cloud requires active management and investment of time from businesses, rather than relying solely on the cloud provider.
Cloud computing provides unparalleled flexibility, cost savings, scalability, and remote collaboration opportunities. Over the past two decades, cloud computing and storage have become integral to enhancing workflow efficiency and meeting data storage requirements. Nevertheless, data can be lost, misconfigured, or face compliance challenges. Neglecting to properly manage data can result in unauthorized access, regulatory penalties, or security breaches.
To safeguard data effectively, businesses must implement robust security practices. Cloud Security Posture Management (CSPM) is a crucial technique that, when integrated into a comprehensive cloud security strategy, can ensure data protection. Let’s delve into how CSPM aids in managing, identifying, and mitigating risks associated with cloud-stored data.
### What is cloud security posture management?
Cloud Security Posture Management (CSPM) is an increasingly popular concept that leverages various security tools to monitor, enhance, and uphold data security in the cloud. These tools scan cloud data configurations, identify misconfigurations, optimize resource allocation, and flag compliance gaps related to data storage.
CSPM has been in existence since 2014 and has assisted numerous businesses in addressing security threats within their cloud infrastructures. By identifying and rectifying poor configurations, insecure access controls, unmonitored assets, and improperly allocated settings, CSPM helps businesses eliminate risks and threats effectively.
### Misconfigurations are a key concern
Cloud misconfigurations are the primary cause of breaches, with various factors contributing to their occurrence:
– Users with excessive privileges
– Forgotten cloud resources
– Inactive default settings
– Inadequately visible assets
– Insufficient logging and monitoring
Businesses relying solely on default cloud provider tools may struggle to prevent such misconfigurations.
### How does CSPM help to secure data?
CSPM tools enable businesses to continuously monitor their cloud assets, promptly identifying misconfigurations, risks, or violations. By generating inventories of cloud resources and configurations, these tools enhance visibility, enabling security teams to detect and address issues proactively. Additionally, CSPM tools conduct compliance checks against industry standards, alerting businesses of any compliance lapses for immediate resolution.
### CSPM tools provide smart automation
CSPM tools automate the auditing process for cloud environments, eliminating the need for manual checks and reducing the risk of human error. By constantly scanning the cloud environment, these tools swiftly flag any detected issues for security teams to investigate. CSPM tools excel in identifying overly permissive access, exposed critical services, inadequately encrypted sensitive data, and publicly accessible cloud storage.
While CSPM tools are not foolproof, they empower security teams to focus on critical issues and streamline the detection and resolution of security threats.
### CSPM and cloud security best practices
For businesses seeking to optimize cloud security, incorporating CSPM and adhering to best practices is essential:
– Establish a comprehensive inventory of cloud assets
– Enforce clear security policies consistently
– Implement continuous monitoring through CSPM tools
– Automate issue resolution processes
– Integrate CSPM tools with other security measures
– Regularly review and assess the effectiveness of security measures
In conclusion, CSPM tools play a vital role in maintaining secure cloud environments by offering constant monitoring, enhanced visibility, and automated risk detection. When combined with other security measures, CSPM tools enable businesses to mitigate cloud security risks effectively.
*Image source: [Unsplash](https://unsplash.com/photos/diagram-k5AxNUn4c5o?utm_source=unsplash&utm_medium=referral&utm_content=creditCopyText)*